OpenAI is growing operations internationally and is expanding into Asia with a new office in Tokyo, Japan. The company says it is collaborating with the Japanese government, local businesses, and research institutions to develop safe AI tools that serve Japan’s unique needs and to unlock new opportunities. OpenAI chose Tokyo as its first Asian office […]
Juicer Milks $5.3 Million Seed Round
SAN FRANCISCO — JUICER, a provider of restaurant revenue management and pricing solutions, has completed a $5.3 million seed round led by York IE. Restaurants are undergoing a profound shift, becoming an e-commerce category thanks to the rise of delivery and digital customer engagement. In this new world, traditional pricing and promotions no longer suffice. […]
Clazar Raises $10 Million Series A
SAN FRANCISCO — Clazar, a company powering software businesses to sell and grow revenue through cloud marketplaces (AWS, Azure, and GCP), has raised a $10 million Series A funding round led by Ridge Ventures and Ensemble VC, with participation from Saurabh Gupta, Managing Partner at DST Global, and existing investors including The General Partnership and […]
Property Brother Drew Scott Invests in Quilt
REDWOOD CITY — Quilt, a smart home climate solution company, has raised $33 million Series A funding round co-led by Energy Impact Partners and Galvanize Climate Solutions, with participation from Lowercarbon Capital, Gradient Ventures, MCJ Collective, Garage Capital, Incite Ventures, and Drew Scott from HGTV’s Property Brothers. Quilt was founded because 20% of U.S. global […]
Avive Scores $56.5 Million
SAN FRANCISCO — Avive Solutions, Inc., a developer of the world’s most advanced connected automated external defibrillator (AED) – the Avive Connect AED – announced the closing of a $56.5 million growth equity financing. The round was led by Questa Capital, Laerdal Million Lives Fund (LMLF), and Catalyst Health Ventures, and welcomed several new investors including RC […]
Uniqus Consultech Reels In $10 Million
SAN JOSE — Uniqus Consultech, a tech-enabled global platform that offers ESG and Accounting & Reporting Consulting, has raised $10 million in Series B funding. The round was led by Nexus Ventures with participation from Sorin Investments. In just over a year of launch, Uniqus has offices in eight cities across the US, India, […]
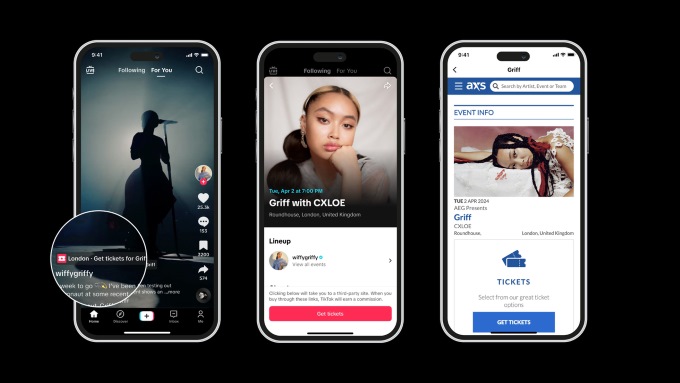
TikTok to Sell Tickets With AXS
TikTok has launched a new partnership with AXS, a leader in global ticketing, to offer fans a new way to discover and buy tickets to live events for their favorite artists. The partnership promises to bring music fans closer to their favorite artists, with the feature live in the US, UK, Sweden and Australia. Now, […]
Apple Airplay Available at IHG Hotels
Guests staying at select properties from IHG Hotels & Resorts, including Kimpton Hotels & Restaurants, Hotel Indigo, Candlewood Suites, and InterContinental Hotels & Resorts, can use AirPlay to privately and securely stream their favorite shows and movies on Apple TV+ and other popular streaming services, listen to personal playlists on Apple Music or other platforms, […]
Two Chairs Sits Down With $72 Million
SAN FRANCISCO — Two Chairs, a behavioral health company, announced the closing of a $72 million Series C equity and debt financing round led by Amplo with Fifth Down Capital, and other investors also participating. Bridge Bank provided the debt financing. This latest round brings the total capital raised to $103M. Two Chairs has grown 8x over the last 36 months and now has […]
Rivos Scores $250 Million Series A-3 Round
SANTA CLARA — Rivos, a RISC-V accelerated platform company targeting data analytics and Generative AI, has raised more than $250 million in its oversubscribed Series A-3 funding round, and Matrix Capital Management, the largest investor in this round, has joined the Board represented by Romit Shah. The funding saw participation from new investors including Intel […]
Anvilogic Closes $45 Million Series C
PALO ALTO — Anvilogic, the industry’s first multi-data platform SIEM, has closed a $45 million Series C funding round, bringing its total funding to date to $85 million since its founding in 2019. The round was led by Evolution Equity Partners, with participation from existing investors Foundation Capital, Cervin Ventures, Myriad Ventures, Point72 Ventures, Outpost Ventures, Stepstone Group, and G Squared. Capitalizing on […]
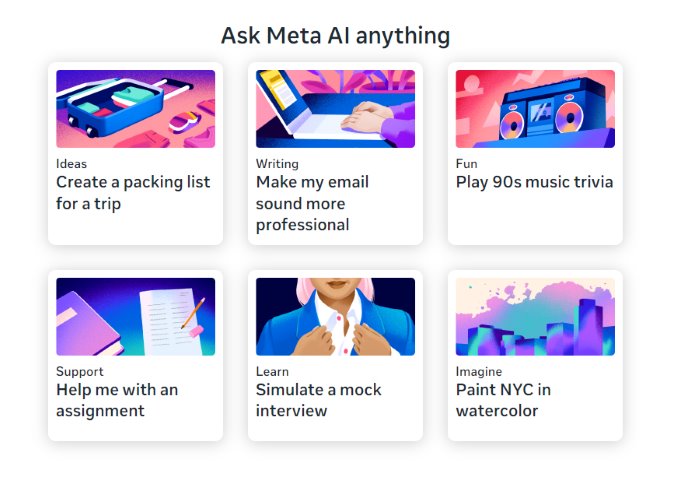
Meta Launches AI Assistant on Facebook, Instagram, Whatsapp
Meta, parent of Facebook, is launching Meta AI built with Llama 3, already on your phone, in your pocket for free. And it’s starting to go global with more features. You can use Meta AI on Facebook, Instagram, WhatsApp and Messenger to get things done, learn, create and connect with the things that matter to […]